Retrieving Cleartext GMSA Passwords from Active Directory
Have you ever wondered how the automatically generated passwords of Group Managed Service Accounts (GMSA) look like? Well, you can fetch them from Active Directory in the same way as Windows Servers do and see yourself. Here is how:
Creating a GMSA
To start experimenting, we need to have a GMSA first, so we create one:
# Create a new KDS Root Key that will be used by DC to generate managed passwords
Add-KdsRootKey -EffectiveTime (Get-Date).AddHours(-10)
# Create a new GMSA
New-ADServiceAccount `
-Name 'SQL_HQ_Primary' `
-DNSHostName 'sql1.adatum.com'
We can check the result in the Active Directory Users and Computers console:
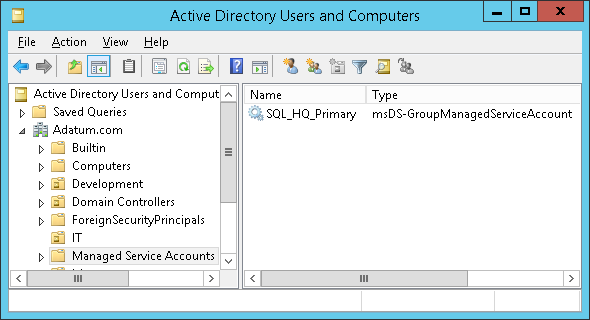
Unfortunately, the built-in GUI will not help us much when working with GMSAs. Although there is a nice 3rd party tool, we will stick to PowerShell.
Setting the Managed Password ACL
Now we need to provide a list of principals that are allowed to retrieve the plaintext password from DCs through LDAP. Normally, we would grant this privilege to one or more servers (members of the same cluster/web farm). But we will grant the privilege to ourselves instead:
Set-ADServiceAccount `
-Identity 'SQL_HQ_Primary' `
-PrincipalsAllowedToRetrieveManagedPassword 'Administrator'
Of course, you should not use the built-in Administrator account in a production environment.
Retrieving the Managed Password
Now comes the fun part:
# We have to explicitly ask for the value of the msDS-ManagedPassword attribute. Even a wildcard (*) would not work.
Get-ADServiceAccount `
-Identity 'SQL_HQ_Primary' `
-Properties 'msDS-ManagedPassword'
<#
Output:
DistinguishedName : CN=SQL_HQ_Primary,CN=Managed Service Accounts,DC=Adatum,DC=com
Enabled : True
msDS-ManagedPassword : {1, 0, 0, 0...}
Name : SQL_HQ_Primary
ObjectClass : msDS-GroupManagedServiceAccount
ObjectGUID : 5f8e24c5-bd21-43a4-95ab-c67939434e81
SamAccountName : SQL_HQ_Primary$
SID : S-1-5-21-3180365339-800773672-3767752645-4102
UserPrincipalName :
#>
Note that until now, we have only used regular, built-in cmdlets from the ActiveDirectory module, courtesy of Microsoft.
Decoding the Managed Password
Let’s have a look at the msDS-ManagedPassword attribute, that has been returned by the command above. It is a constructed attribute, which means that its value is calculated by DC from the KDS root key and the msDS-ManagedPasswordId attribute every time someone asks for it. Although documented, the cryptographic algorithm used is quite complicated. Furthermore, the value of the msDS-ManagedPasswordId gets re-generated every (msDS-ManagedPasswordInterval)-days (30 by default).
We see that the msDS-ManagedPassword attribute of our GMSA contains a sequence of bytes. It is a binary representation of the MSDS-MANAGEDPASSWORD_BLOB data structure, which contains some metadata in addition to the actual password. As there had been no publicly available tool to decode this structure, I have created one myself:
# Save the blob to a variable
$gmsa = Get-ADServiceAccount `
-Identity 'SQL_HQ_Primary' `
-Properties 'msDS-ManagedPassword'
$mp = $gmsa.'msDS-ManagedPassword'
# Decode the data structure using the DSInternals module
ConvertFrom-ADManagedPasswordBlob $mp
<#
Output:
Version : 1
CurrentPassword : 湤ୟɰ橣낔饔ᦺ几᧾ʞꈠ⿕ՔὬ랭뷾햾咶郸�렇ͧ퀟럓몚ꬶ佩䎖∘Ǐ㦗ן뱷鼹⽩Ⲃ⫝咽㠅E䠹鸞왶婰鞪
PreviousPassword :
QueryPasswordInterval : 29.17:15:36.3736817
UnchangedPasswordInterval : 29.17:10:36.3736817
#>
TADA!!! The CurrentPassword property contains the actual cleartext password of the GMSA in question. Why does it look like gibberish? Because it is just 256 bytes of pseudorandom data, interpreted as 128 UTF-16 characters. Good luck writing that on your keyboard. But if we calculate its NT hash, it will match the hash stored in AD.
Conclusion
We have seen that retrieving the value of GMSA passwords is quite easy. But don’t be afraid, there is no security hole in Active Directory. The cleartext password is always passed through an encrypted channel, it is automatically changed on a regular basis and even members of the Domain Admins group are not allowed to retrieve it by default. So do not hesitate and start using the (Group) Managed Service Accounts. They are much safer than using regular accounts for running services.
If you want to play more with this stuff, just grab the DSInternals module. And for developers, the C# code I use to decode the structure can be found on GitHub.
 DSInternals
DSInternals